UGC CBSE NET Nov-III-2017
UGC CBSE NET Nov-III-2017
Note: This paper contains seventy-five (75) objective type questions of two(2)marks each.All question are compulsory.
| Q1➡ In 8085 microprocessor which of the following flag(s) is (are) affected by an arithmetic operation? |
| A ➥ AC flag Only |
| B ➥ CY flag Only |
| C ➥ Z flag Only |
| D ➥ AC, CY, Z flags |
Show Answer With Best Explanation
| Q2➡ In 8085 microprocessor the address bus is of _________ bits. |
| A ➥ 4 |
| B ➥ 8 |
| C ➥ 16 |
| D ➥ 32 |
Show Answer With Best Explanation
| Q3➡ In the architecture of 8085 microprocessor match the following: 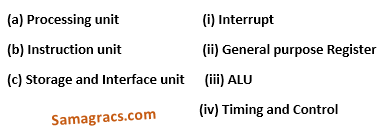 Code: |
| A ➥ (a)-(iv), (b)-(i), (c)-(ii) |
| B ➥ (a)-(iii), (b)-(iv), (c)-(ii) |
| C ➥ (a)-(ii), (b)-(iii), (c)-(i) |
| D ➥ (a)-(i), (b)-(ii), (c)-(iv) |
Show Answer With Best Explanation
| Q4➡ Which of the following addressing mode is best suited to access elements of an array of contiguous memory locations ? |
| A ➥ Indexed addressing mode |
| B ➥ Base Register addressing mode |
| C ➥ Relative address mode |
| D ➥ Displacement mode |
Show Answer With Best Explanation
| Q5➡ Which of the following is correct statement ? |
| A ➥ In memory – mapped I/O, the CPU can manipulate I/O data residing in interface registers that are not used to manipulate memory words. |
| B ➥ The isolated I/O method isolates memory and I/O addresses so that memory address range is not affected by interface address assignment. |
| C ➥ In asynchronous serial transfer of data the two units share a common clock. |
| D ➥ In synchronous serial transmission of data the two units have different clocks. |
Show Answer With Best Explanation
| Q6➡ A microinstruction format has micro-ops field which is divided into three subfields F1, F2, F3 each having seven distinct micro-operations, condition field CD for four status bits, branch field BR having four options used in conjunction with address field ADF. The address space is of 128 memory locations. The size of micro-instruction is: |
| A ➥ 17 |
| B ➥ 20 |
| C ➥ 24 |
| D ➥ 32 |
Show Answer With Best Explanation
| Q7➡ Consider the following four schedules due to three transactions (indicated by the subscript) using read and write on a data item X, denoted by r(X) and w(X) respectively. Which one of them is conflict serializable ? S1: r1(X); r2(X); w1(X); r3(X); w2(X) S2: r2(X); r1(X); w2(X); r3(X); w1(X) S3: r3(X); r2(X); r1(X); w2(X); w1(X) S4: r2(X); w2(X); r3(X); r1(X); w1(X) |
| A ➥ S1 |
| B ➥ S2 |
| C ➥ S3 |
| D ➥ S4 |
Show Answer With Best Explanation
| Q8➡ Suppose a database schedule S involves transactions T1, T2,____________Tn. Consider the precedence graph of S with vertices representing the transactions and edges representing the conflicts. If S is serializable, which one of the following orderings of the vertices of the precedence graph is guaranteed to yield a serial schedule ? |
| A ➥ Topological order |
| B ➥ Depth – first order |
| C ➥ Breadth – first order |
| D ➥ Ascending order of transaction indices |
Show Answer With Best Explanation
| Q9➡ If every non-key attribute is functionally dependent on the primary key, then the relation is in____________. |
| A ➥ First normal form |
| B ➥ Second normal form |
| C ➥ Third normal form |
| D ➥ Fourth normal form |
Show Answer With Best Explanation
| Q10➡ Consider a relation R (A, B, C, D, E, F, G, H), where each attribute is atomic, and following functional dependencies exist. CH → G A → BC B → CFH E → A F → EG The relation R is___________. |
| A ➥ in 1NF but not in 2NF |
| B ➥ in 2NF but not in 3NF |
| C ➥ in 3NF but not in BCNF |
| D ➥ in BCNF |
Show Answer With Best Explanation
| Q11➡ Given two relations R1(A, B) and R2(C, D), the result of following query Select distinct A, B from R1, R2 is guaranteed to be same as R1 provided one of the following condition is satisfied. |
| A ➥ R1 has no duplicates and R2 is empty. |
| B ➥ R1 has no duplicates and R2 is non – empty. |
| C ➥ Both R1 and R2 have no duplicates. |
| D ➥ R2 has no duplicates and R1 is non – empty. |
Show Answer With Best Explanation
| Q12➡ Consider a schema R(A, B, C, D) and following functional dependencies. A → B B → C C → D D → B Then decomposition of R into R1(A, B), R2(B, C) and R3(B, D) is____________. |
| A ➥ Dependency preserving and lossless join. |
| B ➥ Lossless join but not dependency preserving. |
| C ➥ Dependency preserving but not lossless join. |
| D ➥ Not dependency preserving and not lossless join. |
Show Answer With Best Explanation
| Q13➡Computer Graphics Which of the following is not a component of Memory tube display ? |
| i ➥ Flooding gun |
| ii ➥ Collector |
| iii ➥ Ground |
| iv ➥ Liquid Crystal |
Show Answer With Best Explanation
| Q14➡Computer Graphics Which of the following is not true in case of Oblique Projections? |
| i ➥ Parallel projection rays are not perpendicular to the viewing plane. |
| ii ➥ Parallel lines in space appear parallel on the final projected image. |
| iii ➥ Used exclusively for pictorial purposes rather than formal working drawings. |
| iv ➥ Projectors are always perpendicular to the plane of projection. |
Show Answer With Best Explanation
| Q15➡Computer Graphics With respect to CRT, the horizontal retrace is defined as: |
| i ➥ The path an electron beam takes when returning to the left side of the CRT. |
| ii ➥ The path an electron beam takes when returning to the right side of the CRT. |
| iii ➥ The technique of turning the electron beam off while retracing. |
| iv ➥ The technique of turning the electron beam on/off while retracing. |
Show Answer With Best Explanation
| Q16➡ Computer Graphics Find the equation of the circle x2+y2=1 in terms of x’y’ coordinates, assuming that the xy coordinate system results from a scaling of 3 units in the x’ direction and 4 units in the y’ direction. |
| i ➥ 3(x’)2 + 4(y’)2 = 1 |
| ii ➥ (x’/3)2 + (y’/4)2 = 1 |
| iii ➥ (3x’)2 + 4(y’)2 = 1 |
| iv ➥ 1/3(x’)2 + 1/4(y’)2 = 1 |
Show Answer With Best Explanation
| Q17➡ Computer Graphics Find the normalization transformation that maps a window whose lower left corner is at (1, 1) and upper right corner is at (3, 5) onto a viewport that is the entire normalized device screen. |
i ➥ 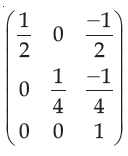 |
ii ➥ 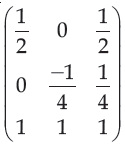 |
iii ➥ 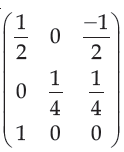 |
iv ➥ 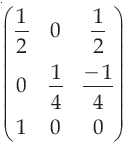 |
Show Answer With Best Explanation
| Q8➡ | Computer Graphics The three aspects of Quantization, programmers generally concerned with are: |
| i ➥ Coding error, Sampling rate and Amplification |
| ii ➥ Sampling rate, Coding error and Conditioning |
| iii ➥ Sampling rate, Aperture time and Coding error |
| iv ➥ Aperture time, Coding error and Strobing |
Show Answer With Best Explanation
| More Discussion | Explanation On YouTube | Learn Topic Wise | Help-Line |
| Q19➡ The logic of pumping lemma is an example of______________. |
| A ➥ iteration |
| B ➥ recursion |
| C ➥ the divide and conquer principle |
| D ➥ the pigeonhole principle |
Show Answer With Best Explanation
| Q20➡ Heap allocation is required for languages that |
| A ➥ use dynamic scope rules |
| B ➥ support dynamic data structures |
| C ➥ support recursion |
| D ➥ support recursion and dynamic data structures |
Show Answer With Best Explanation
| Q21➡ Pumping lemma for regular language is generally used for proving: |
| A ➥ whether two given regular expressions are equivalent |
| B ➥ a given grammar is ambiguous |
| C ➥ a given grammar is regular |
| D ➥ a given grammar is not regular |
Show Answer With Best Explanation
| Q22➡ Which of the following problems is undecidable? |
| A ➥ To determine if two finite automata are equivalent |
| B ➥ Membership problem for context free grammar |
| C ➥ Finiteness problem for finite automata |
| D ➥ Ambiguity problem for context free grammar |
Show Answer With Best Explanation
| Q23➡ Finite state machine can recognize language generated by__________. |
| A ➥ Only context free grammar |
| B ➥ Only context sensitive grammar |
| C ➥ Only regular grammar |
| D ➥ any unambiguous grammar |
Show Answer With Best Explanation
| Q24➡ The language L = {ai b ci │ i >= 0} over the alphabet {a, b, c} is: |
| A ➥ a regular language. |
| B ➥ not a deterministic context free language but a context free language. |
| C ➥ recursive and is a deterministic context free language. |
| D ➥ not recursive. |
Show Answer With Best Explanation
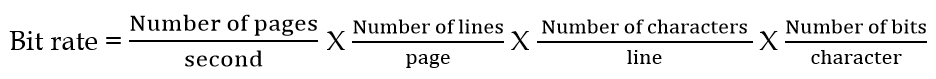
| Question 25➡ | Computer Network Suppose we want to download text documents at the rate of 100 pages per second. Assume that a page consists of an average of 24 lines with 80 characters in each line. What is the required bit rate of the channel? |
| i ➥ 192 kbps |
| ii ➥ 512 kbps |
| iii ➥ 1.248 Mbps |
| iv ➥ 1.536 Mbps |
Show Answer With Best Explanation
| More Discussion | Explanation On YouTube | Numerical | Help-Line |
| Question 26➡ | Computer Network Quadrature Amplitude Modulation means changing both: |
| i ➥ Frequency and phase of the carrier. |
| ii ➥ Frequency and Amplitude of the carrier. |
| iii ➥ Amplitude and phase of the carrier. |
| iv ➥ Amplitude and Wavelength of the carrier. |
Show Answer With Best Explanation
| More Discussion | Explanation On YouTube | Learn Topic Wise | Help-Line |
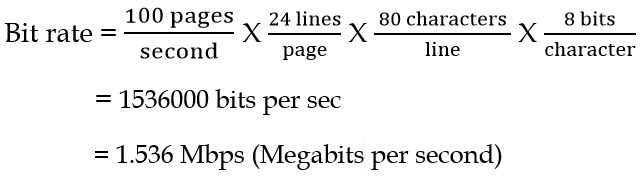
| Question 27➡ | Computer Network If a file consisting of 50,000 characters takes 40 seconds to send, then the data rate is_______. |
| i ➥ 1 kbps |
| ii ➥ 1.25 kbps |
| iii ➥ 2 kbps |
| iv ➥ 10 kbps |
Show Answer With Best Explanation
| More Discussion | Explanation On YouTube | Numerical | Help-Line |
| Question 28➡ | Computer Network Match the following: 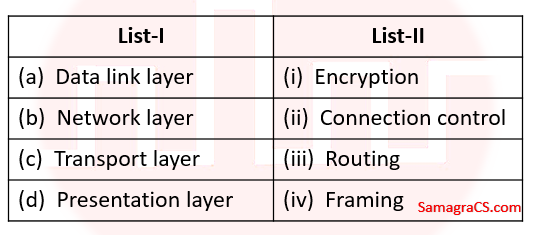 |
| i ➥ (a)-(iv), (b)-(iii), (c)-(i), (d)-(ii) |
| ii ➥ (a)-(iii), (b)-(iv), (c)-(ii), (d)-(i) |
| iii ➥ (a)-(iv), (b)-(ii), (c)-(iii), (d)-(i) |
| iv ➥ (a)-(iv), (b)-(iii), (c)-(ii), (d)-(i) |
Show Answer With Best Explanation
| More Discussion | Explanation On YouTube | Learn Topic Wise | Help-Line |
| Question 29➡ | Computer Network The address of a class B host is to be split into subnets with a 6 – bit subnet number. What is the maximum number of subnets and maximum number of hosts in each subnet? |
| i ➥ 62 subnets and 1022 hosts |
| ii ➥ 64 subnets and 1024 hosts |
| iii ➥ 62 subnets and 254 hosts |
| iv ➥ 64 subnets and 256 hosts |
Show Answer With Best Explanation
| More Discussion | Explanation On YouTube | Learn Topic Wise | Help-Line |
| Question 30➡ | Computer Network Which of the following statements are true? (a) The fragmentation fields in the base header section of IPv4 have moved to the fragmentation extension header in IPv6. (b) The authentication extension header is new in IPv6. (c) The record route option is not implemented in IPv6. |
| i ➥ (a) and (b) Only |
| ii ➥ (b) and (c) Only |
| iii ➥ (a) and (c) Only |
| iv ➥ (a), (b) and (c) |
Show Answer With Best Explanation
| More Discussion | Explanation On YouTube | Learn Topic Wise | Help-Line |
| Q31➡ Consider a full binary tree with n internal nodes, internal path length i, and external path length e. The internal path length of a full binary tree is the sum, taken over all nodes of the tree, of the depth of each node. Similarly, the external path length is the sum, taken over all leaves of the tree, of the depth of each leaf. Which of the following is correct for the full binary tree? |
| A ➥ e = i+n |
| B ➥ e = i+2n |
| C ➥ e = 2i+n |
| D ➥ e = 2n+i |
Show Answer With Best Explanation
| Q32➡ You are given a sequence of n elements to sort. The input sequence consists of n/k subsequences, each containing k elements. The elements in a given subsequence are all smaller than the elements in the succeeding subsequence and larger than the elements in the preceding subsequence. Thus, all that is needed to sort the whole sequence of length n is to sort the k elements in each of the n/k subsequences. The lower bound on the number of comparisons needed to solve this variant of the sorting problem is |
| A ➥ Ω(n) |
| B ➥ Ω(n/k) |
| C ➥ Ω(nlogk ) |
| D ➥ Ω(n/k log n/k) |
Show Answer With Best Explanation
| Q33➡ T(n)= 8T (n/2)+Cn, if n>1 = b, if n=1 Consider the recurrence relation: Where b and c are constants. The order of the algorithm corresponding to above recurrence relation is: |
| A ➥ n |
| B ➥ n2 |
| C ➥ n log n |
| D ➥ n3 |
Show Answer With Best Explanation
| Q34➡ Consider the following two sequences : X = < B, C, D, C, A, B, C > and Y = < C, A, D, B, C, B > The length of longest common subsequence of X and Y is : |
| A ➥ 5 |
| B ➥ 3 |
| C ➥ 4 |
| D ➥ 2 |
Show Answer With Best Explanation
| Q35➡ A text is made up of the characters a, b, c, d, e each occurring with the probability 0.11, 0.40, 0.16, 0.09 and 0.24 respectively. The optimal Huffman coding technique will have the average length of: |
| A ➥ 2.40 |
| B ➥ 2.16 |
| C ➥ 2.26 |
| D ➥ 2.15 |
Show Answer With Best Explanation
| Q36➡ An undirected graph G (V, E) contains n (n > 2) nodes named V1 , V2 ,……,Vn. Two nodes vi and vj are connected if and only if 0 <│i−j│≤2. Each edge (Vi , Vj ) is assigned a weight i+j. The cost of the minimum spanning tree of such a graph with 10 nodes is: |
| A ➥ 88 |
| B ➥ 91 |
| C ➥ 49 |
| D ➥ 21 |
Show Answer With Best Explanation
| Q37➡ An XML document that adheres to syntax rules specified by XML 1.0 specification in that it must satisfy both physical and logical structured, is called: |
| A ➥ Well – formed |
| B ➥ Reasonable |
| C ➥ Valid |
| D ➥ Sophisticated |
Show Answer With Best Explanation
| Q38➡ Which of the following statement(s) is/are TRUE regarding Java Servlets ? (a) A Java Servlet is a server-side component that runs on the web server and extends the capabilities of a server. (b) A Servlet can use the user interface classes like AWT or Swing. |
| A ➥ Only (a) is TRUE. |
| B ➥ Only (b) is TRUE. |
| C ➥ Both (a) and (b) are TRUE. |
| D ➥ Neither (a) nor (b) is TRUE. |
Show Answer With Best Explanation
Q39➡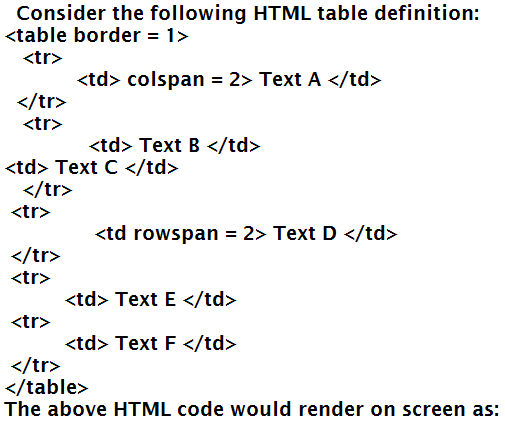 |
A ➥ 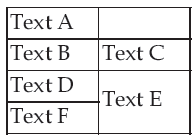 |
B ➥  |
C ➥  |
D ➥  |
Show Answer With Best Explanation
| Q40➡ Which of the following statements is/are TRUE ? (a) In HTML, character entities are used to incorporate external content into a web page, such as images. (b) Once a web server returns a cookie to a browser, the cookie will be included in all future requests from the browser to the same server. |
| A ➥ Only (a) is TRUE. |
| B ➥ Only (b) is TRUE. |
| C ➥ Both (a) and (b) are TRUE. |
| D ➥ Neither (a) nor (b) is TRUE. |
Show Answer With Best Explanation
| Q41➡ Which of the following statements is/are TRUE regarding JAVA ? (a) Constants that cannot be changed are declared using the ‘static’ keyword. (b) A class can only inherit one class but can implement multiple interfaces. |
| A ➥ Only (a) is TRUE. |
| B ➥ Only (b) is TRUE. |
| C ➥ Both (a) and (b) are TRUE. |
| D ➥ Neither (a) nor (b) are TRUE. |
Show Answer With Best Explanation
| Q42➡ What is the output of the following JAVA program ? Class Test { public static void main(String[] args) { Test obj = new Test(); obj.start(); } void start() { String stra = ”do”; String strb = method(stra); System.out.print(“: ”+stra + strb); } String method(String stra) { stra = stra + ”good”; System.out.print(stra); return“ good”; } } |
| A ➥ dogood : dogoodgood |
| B ➥ dogood : gooddogood |
| C ➥ dogood : dodogood |
| D ➥ dogood : dogood |
Show Answer With Best Explanation
| Q43➡ Statistical software quality assurance in software engineering involves___________. |
| A ➥ using sampling in place of exhaustive testing of software. |
| B ➥ surveying customers to find out their opinions about product quality. |
| C ➥ tracing each defect to its underlying cause, isolating the vital few causes, and moving to correct them. |
| D ➥ tracing each defect to its underlying causes, and using the Pareto principle to correct each problem found. |
Show Answer With Best Explanation
| Q44➡ Which of the following statements is/are FALSE with respect to software testing ? S1 : White-box tests are based on specifications; better at telling whether program meets specification, better at finding errors of omission. S2 : Black- box tests are based on code; better for finding crashes, out of bounds errors, file not closed errors. S3 : Alpha testing is conducted at the developer’s site by a team of highly skilled testers for software that is developed as a product to be used by many customers. |
| A ➥ Only S1 and S2 are FALSE. |
| B ➥ Only S1 and S3 are FALSE. |
| C ➥ Only S2 and S3 are FALSE. |
| D ➥ All of S1, S2, and S3 are FALSE. |
Show Answer With Best Explanation
| Q45➡ A signal processor software is expected to operate for 91.25 days after repair, and the mean software repair time is expected to be 5 minutes. Then, the availability of the software is: |
| A ➥ 96.9862% |
| B ➥ 97.9862% |
| C ➥ 98.9962% |
| D ➥ 99.9962% |
Show Answer With Best Explanation
| Q46➡ Consider the method mcq ( ): int mcq(boolean a, boolean b, boolean c, boolean d) { int ans=1; if(a) { ans = 2; } else if (b) { ans = 3; } else if (c) { if (d) { ans = 4; } return ans; } if M1 = Number of tests to exhaustively test mcq( ); M2 = Minimum number of tests to achieve full statement coverage for mcq( ); and M3 = Minimum number of tests to achieve full branch coverage for mcq( ); then (M1, M2, M3) =_______________. |
| A ➥ (16, 3, 5) |
| B ➥ (8, 5, 3) |
| C ➥ (8, 3, 5) |
| D ➥ (16, 4, 4) |
Show Answer With Best Explanation
| Q47➡ A simple stand – alone software utility is to be developed in ‘C’ programming by a team of software experts for a computer running Linux and the overall size of this software is estimated to be 20,000 lines of code. Considering (a, b) = (2.4, 1.05) as multiplicative and exponention factor for the basic COCOMO effort estimation equation and (c, d) = (2.5, 0.38) as multiplicative and exponention factor for the basic COCOMO development time estimation equation, approximately how long does the software project take to complete ? |
| A ➥ 10.52 months |
| B ➥ 11.52 months |
| C ➥ 12.52 months |
| D ➥ 14.52 months |
Show Answer With Best Explanation
| Q48➡ In Software Configuration Management (SCM), which of the following is a use-case supported by standard version control systems ? (A) Managing several versions or releases of a software (B) Filing bug reports and tracking their progress (C) Allowing team members to work in parallel (D) Identifying when and where a regression occurred. |
| A ➥ Only (A), (C), and (D) |
| B ➥ Only (A), (B), and (C) |
| C ➥ Only (A), (B), and (D) |
| D ➥ Only (B), (C), and (D) |
Show Answer With Best Explanation
| Q49➡ Consider the following four processes with the arrival time and length of CPU burst given in milliseconds :  The average waiting time for preemptive SJF scheduling algorithm is_______. |
| A ➥ 6.5 |
| B ➥ 7.5 |
| C ➥ 6.75 |
| D ➥ 7.75 |
Show Answer With Best Explanation
| Q50➡ Consider a virtual page reference string 7, 0, 1, 2, 0, 3, 0, 4, 2, 3, 0, 3, 2, 1, 2, 0, 1, 7, 0, 1 Suppose a demand paged virtual memory system running on a computer system such that the main memory has 3 page frames. Then________ page replacement algorithm has minimum number of page faults. |
| A ➥ FIFO |
| B ➥ LIFO |
| C ➥ LRU |
| D ➥ Optimal |
Show Answer With Best Explanation
| Q51➡ User level threads are threads that are visible to the programmer and are unknown to the kernel. The operating system kernel supports and manages kernel level threads. Three different types of models relate user and kernel level threads. Which of the following statements is/are true ? (A)- (i) The Many – to – one model maps many user threads to one kernel thread (ii) The one – to – one model maps one user thread to one kernel thread (iii) The many – to – many model maps many user threads to smaller or equal kernel threads (B)- (i) Many – to – one model maps many kernel threads to one user thread (ii) One – to – one model maps one kernel thread to one user thread (iii) Many – to – many model maps many kernel threads to smaller or equal user threads |
| A ➥ (A) is true; (B) is false |
| B ➥ (A) is false; (B) is true |
| C ➥ Both (A) and (B) are true |
| D ➥ Both (A) and (B) are false |
Show Answer With Best Explanation
| Q52➡ Consider a system with five processes P0 through P4 and three resource types A, B and C. Resource type A has seven instances, resource type B has two instances and resource type C has six instances suppose at time T0 we have the following allocation. 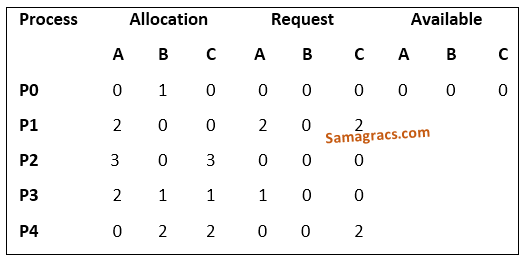 If we implement Deadlock detection algorithm we claim that system is_____. |
| A ➥ Semaphore |
| B ➥ Deadlock state |
| C ➥ Circular wait |
| D ➥ Not in deadlock state |
Show Answer With Best Explanation
| Q53➡ Consider a disk queue with requests for I/O to blocks on cylinders 98, 183, 37, 122, 14, 124, 65, 67 Suppose SSTF disk scheduling algorithm implemented to meet the requests then the total number of head movements are_____if the disk head is initially at 53. |
| A ➥ 224 |
| B ➥ 248 |
| C ➥ 236 |
| D ➥ 240 |
Show Answer With Best Explanation
| Q54➡ The Bounded buffer problem is also known as________. |
| A ➥ Producer – consumer problem |
| B ➥ Reader – writer problem |
| C ➥ Dining Philosophers problem |
| D ➥ Both (2) and (3) |
Show Answer With Best Explanation
| Q55➡ In Artificial Intelligence (AI), which agent deals with happy and unhappy state? |
| A ➥ Simple reflex agent |
| B ➥ Model based agent |
| C ➥ Learning agent |
| D ➥ Utility based agent |
Show Answer With Best Explanation
| Q56➡ If b is the branching factor and m is the maximum depth of the search tree, what is the space complexity of greedy search? |
| A ➥ O(b+m) |
| B ➥ O(bm) |
| C ➥ O(bm) |
| D ➥ O(mb) |
Show Answer With Best Explanation
| Q57➡ Let P, Q, R and S be Propositions. Assume that the equivalences P ⇔ (Q ∨ ¬ Q) and Q ⇔ R hold. Then the truth value of the formula (P ∧ Q) ⇒ ((P ∧ R) ∨ S) is always: |
| A ➥ True |
| B ➥ False |
| C ➥ Same as truth table of Q |
| D ➥ Same as truth table of S |
Show Answer With Best Explanation
| Q58➡ “If X, then Y unless Z” is represented by which of the following formulae in propositional logic? |
| A ➥ (X ∧ Y) → ¬ Z |
| B ➥ (X ∧ ¬ Z) → Y |
| C ➥ X → (Y ∧ ¬ Z) |
| D ➥ Y → (X ∧ ¬ Z) |
Show Answer With Best Explanation
| Q59➡ Consider the following two well-formed formulas in propositional logic. F1 : P ⇒ ¬ P F2 : (P ⇒ ¬ P) ∨ (¬ P ⇒ P) Which of the following statements is correct? |
| A ➥ F1 is Satisfiable, F2 is valid |
| B ➥ F1 is unsatisfiable, F2 is Satisfiable |
| C ➥ F1 is unsatisfiable, F2 is valid |
| D ➥ F1 and F2 both are Satisfiable |
Show Answer With Best Explanation
| Q60➡ Standard planning algorithms assume environment to be________. |
| A ➥ Both deterministic and fully observable |
| B ➥ Neither deterministic nor fully observable |
| C ➥ Deterministic but not fully observable |
| D ➥ Not deterministic but fully observable |
Show Answer With Best Explanation
| Q61➡ Which of the following statements is not correct? |
| A ➥ Every recursive language is recursively enumerable. |
| B ➥ L = {0n1n 0n │n=1, 2 , 3, ….} is recursively enumerable. |
| C ➥ Recursive languages are closed under intersection. |
| D ➥ Recursive languages are not closed under intersection. |
Show Answer With Best Explanation
| Q62➡ Context free grammar is not closed under: |
| A ➥ Concatenation |
| B ➥ Complementation |
| C ➥ Kleene Star |
| D ➥ Union |
Show Answer With Best Explanation
| Q63➡ Consider the following languages: L1 = {am bn │ m ≠ n} L2 = {am bn │ m = 2n+1} L3 = {am bn │ m ≠ 2n} Which one of the following statement is correct ? |
| A ➥ Only L1 and L2 are context free languages |
| B ➥ Only L1 and L3 are context free languages |
| C ➥ Only L2 and L3 are context free languages |
| D ➥ L1, L2 and L3 are context free languages |
Show Answer With Best Explanation
| Q64➡ A 4*4 DFT matrix is given by : 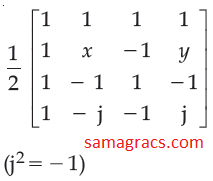 Where values of x and y are____,____respectively. |
| A ➥ 1, −1 |
| B ➥ −1, 1 |
| C ➥ −j, j |
| D ➥ j, −j |
Show Answer With Best Explanation
| Q65➡ Entropy of a discrete random variable with possible values {x1, x2, …, xn} and probability density function P(X) is : 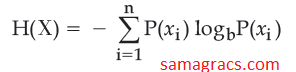 The value of b gives the units of entropy. The unit for b=10 is : |
| A ➥ bits |
| B ➥ bann |
| C ➥ nats |
| D ➥ deca |
Show Answer With Best Explanation
| Q66➡ For any binary (n, h) linear code with minimum distance (2t+1) or greater 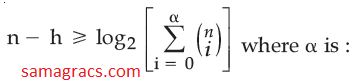 |
| A ➥ 2t+1 |
| B ➥ t+1 |
| C ➥ t |
| D ➥ t-1 |
Show Answer With Best Explanation
| Q67➡ Which of the following is a valid reason for causing degeneracy in a transportation problem ? Here m is no. of rows and n is no. of columns in transportation table |
| A ➥ When the number of allocations is m+n−1. |
| B ➥ When two or more occupied cells become unoccupied simultaneously. |
| C ➥ When the number of allocations is less than m+n−1. |
| D ➥ When a loop cannot be drawn without using unoccupied cells, except the starting cell of the loop. |
Show Answer With Best Explanation
| Q68➡ Consider the following LPP : Max Z = 15x1 + 10x2 Subject to the constraints 4x1 + 6x2 ≤ 360 3x1 + 0x2 ≤ 180 0x1 + 5x2 ≤ 200 x1, x2 / 0 The solution of the LPP using Graphical solution technique is : |
| A ➥ x1=60, x2=0 and Z=900 |
| B ➥ x1=60, x2=20 and Z=1100 |
| C ➥ x1=60, x2=30 and Z=1200 |
| D ➥ x1=50, x2=40 and Z=1150 |
Show Answer With Best Explanation
| Q69➡ Consider the following LPP : Min Z = 2x1 + x2 + 3x3 Subject to : x1 − 2x2 + x3 ≥ 4 2x1 + x2 + x3 ≤ 8 x1 − x3 ≥ 0 x1, x2, x3 ≥ 0 The solution of this LPP using Dual Simplex Method is : |
| A ➥ x1=0, x2=0, x3=3 and Z=9 |
| B ➥ x1=0, x2=6, x3=0 and Z=6 |
| C ➥ x1=4, x2=0, x3=0 and Z=8 |
| D ➥ x1=2, x2=0, x3=2 and Z=10 |
Show Answer With Best Explanation
Q70➡ |
A ➥ 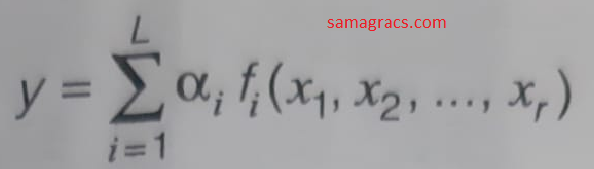 |
B ➥  |
C ➥ 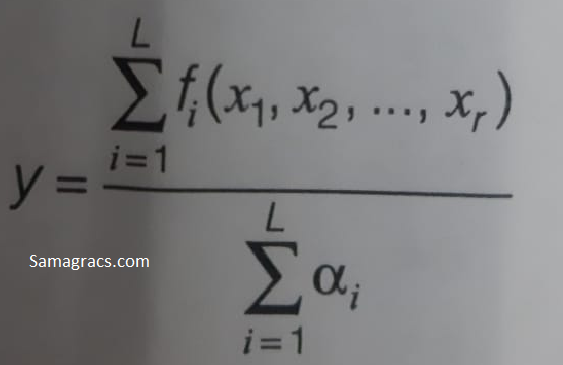 |
D ➥ 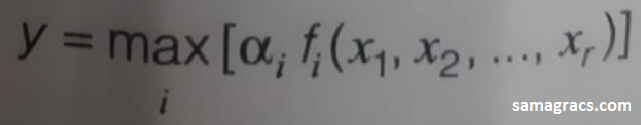 |
Show Answer With Best Explanation
| Q71➡ Consider a single perceptron with sign activation function. The perceptron is represented by weight vector [0.4 −0.3 0.1]t and a bias θ = 0. If the input vector to the perceptron is X = [0.2 0.6 0.5] then the output of the perceptron is: |
| A ➥ 1 |
| B ➥ 0 |
| C ➥ -0.25 |
| D ➥ -1 |
Show Answer With Best Explanation
| Q72➡ The Sigmoid activation function f(t) is defined as: |
A ➥ 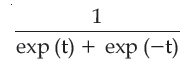 |
| B ➥ |
C ➥ 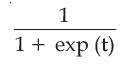 |
D ➥ 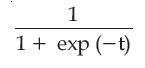 |
Show Answer With Best Explanation
| Q73➡ Consider the following statements : (A) . UNIX provides three types of permissions Read Write Execute (B). UNIX provides three sets of permissions permission for owner permission for group permission for others Which of the above statement/s is/are true ? |
| A ➥ only (a) |
| B ➥ only (b) |
| C ➥ Both (a) and (b) |
| D ➥ Neither (a) nor (b) |
Show Answer With Best Explanation
| Question 74➡ | NTA UGC NET November 2017 Paper-3 Which of the following routing technique / techniques is / are used in distributed systems ? (a) Fixed Routing (b) Virtual Routing (c) Dynamic Routing |
| i ➥ (a) only |
| ii ➥ (a) and (b) only |
| iii ➥ (c) only |
| iv ➥ All (a), (b), (C) |
Show Answer With Best Explanation
| More Discussion | Explanation On YouTube | Learn Topic Wise | Help-Line |
| Q75➡ Match the following WINDOWS system calls and UNIX system calls with reference to process control and File manipulation. 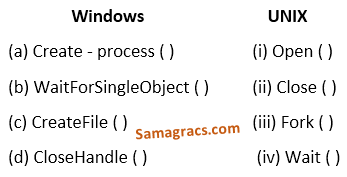 |
| A ➥ (a)-(iii), (b)-(iv), (c)-(i), (d)-(ii) |
| B ➥ (a)-(iv), (b)-(iii), (c)-(i), (d)-(ii) |
| C ➥ (a)-(iv), (b)-(iii), (c)-(ii), (d)-(i) |
| D ➥ (a)-(iii), (b)-(iv), (c)-(ii), (d)-(i) |